Vulnversity

Task 1 - Deploy the machine
Task 2 - Reconnaissance
2.1 - Scan the box; how many ports are open?
2.2 - What version of the squid proxy is running on the machine?
2.3 - How many ports will Nmap scan if the flag -p-400 was used?
2.4 - What is the most likely operating system this machine is running?
2.5 - What port is the web server running on?
Task 3 - Locating directories using Gobuster
3.1 - What is the directory that has an upload form page?
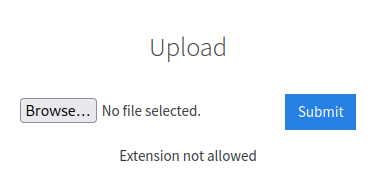
Task 4 - Compromise the Webserver
4.1 - What common file type you'd want to upload to exploit the server is blocked? Try a couple to find out.